Overflow Conference (Buffalo) Recap | What a move of God we experienced in buffalo, New York! Thank you Curtis N Ani Minniefield and Sword of the Spirit Ministries for allowing us to
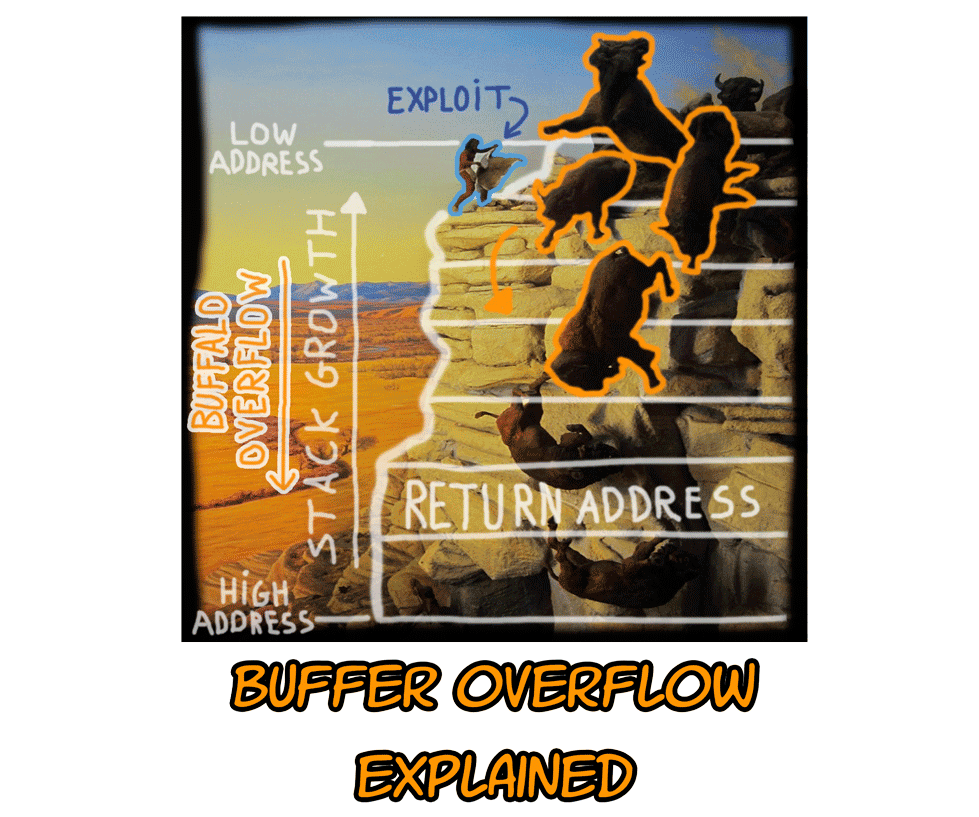
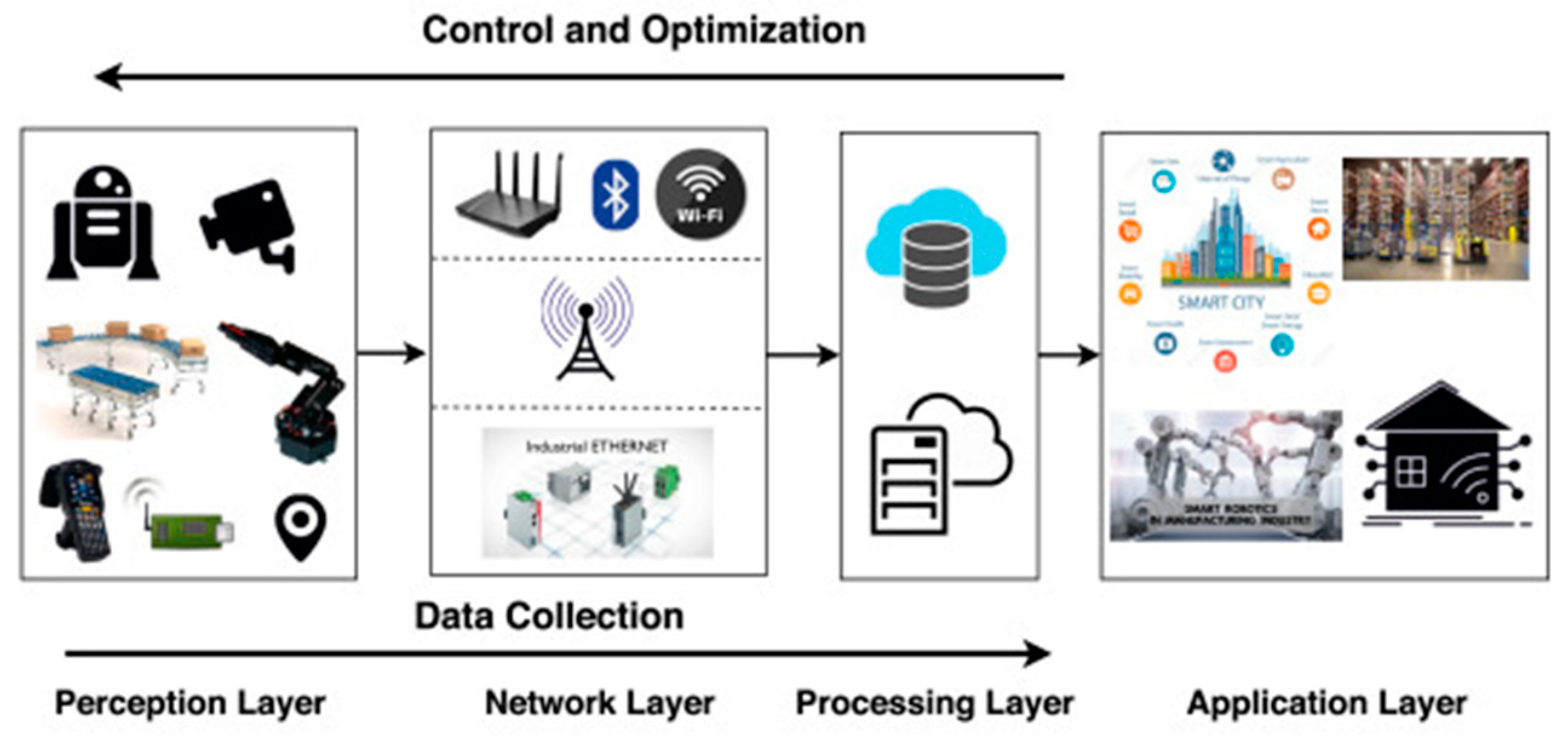
Buffer Overflow Network Security Computer Network Attack, PNG, 1240x1346px, Buffer Overflow, Area, Attack, Computer Network, Computer

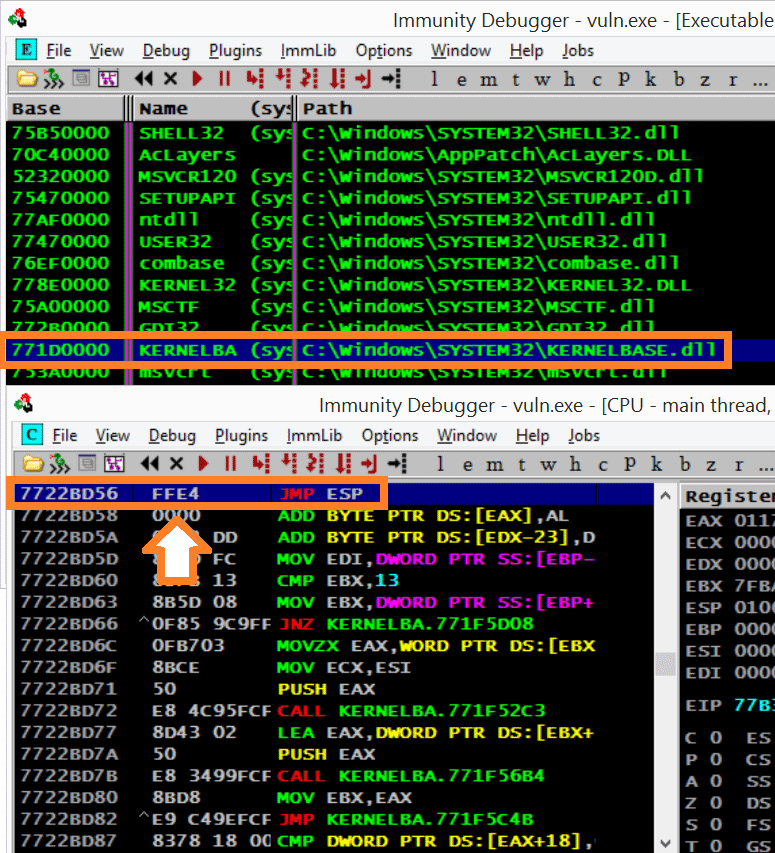
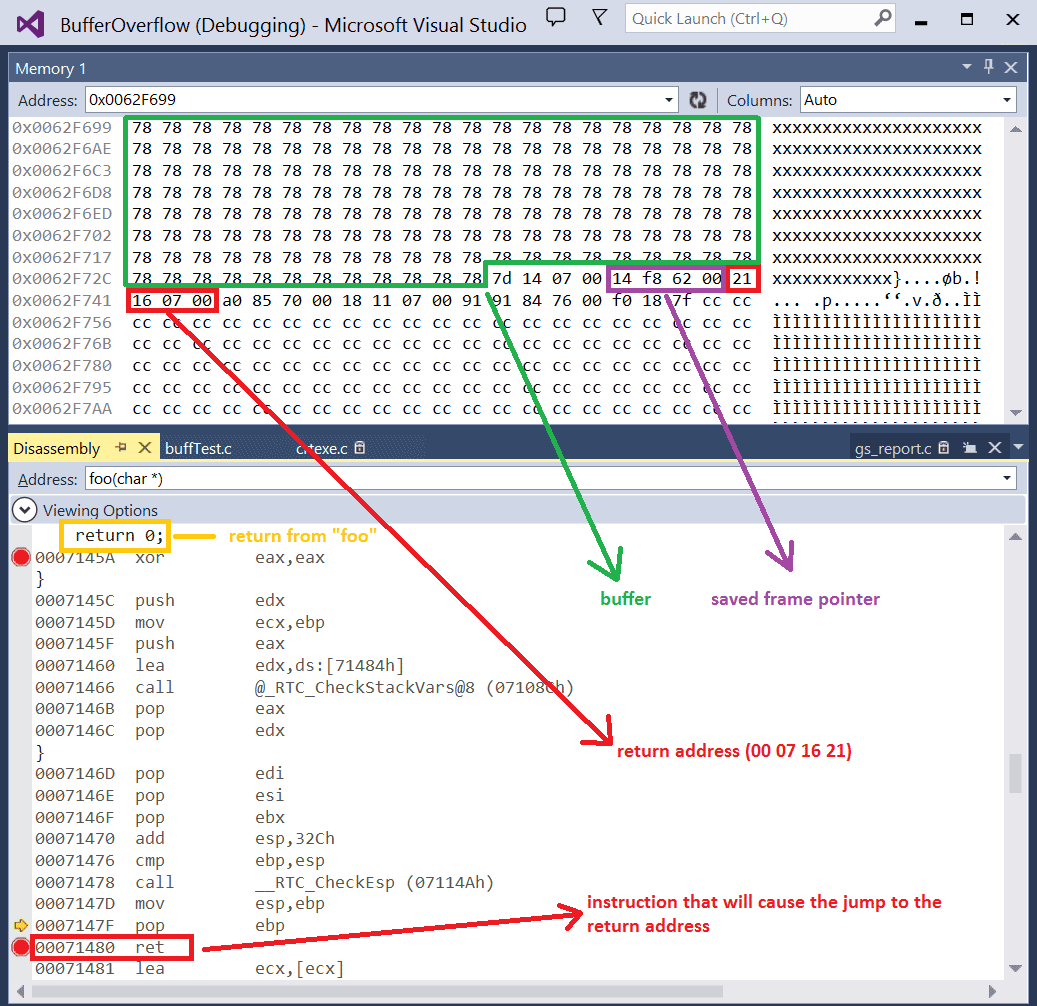
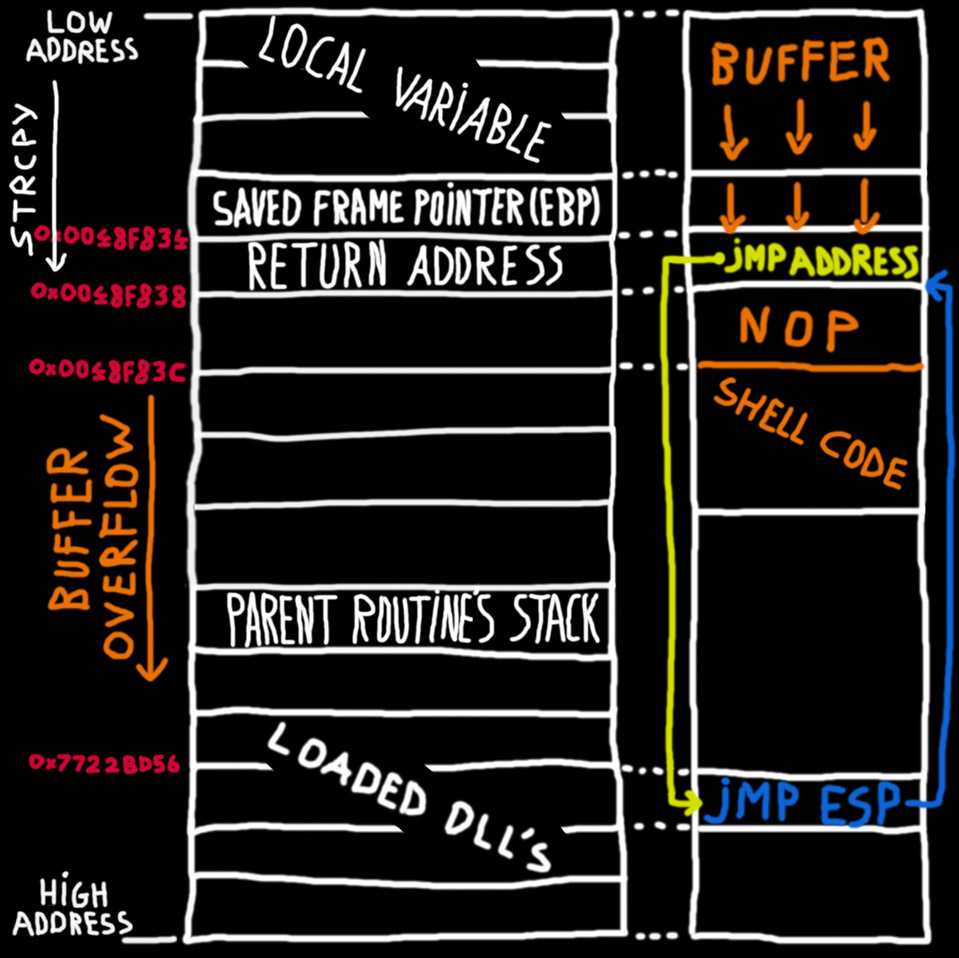
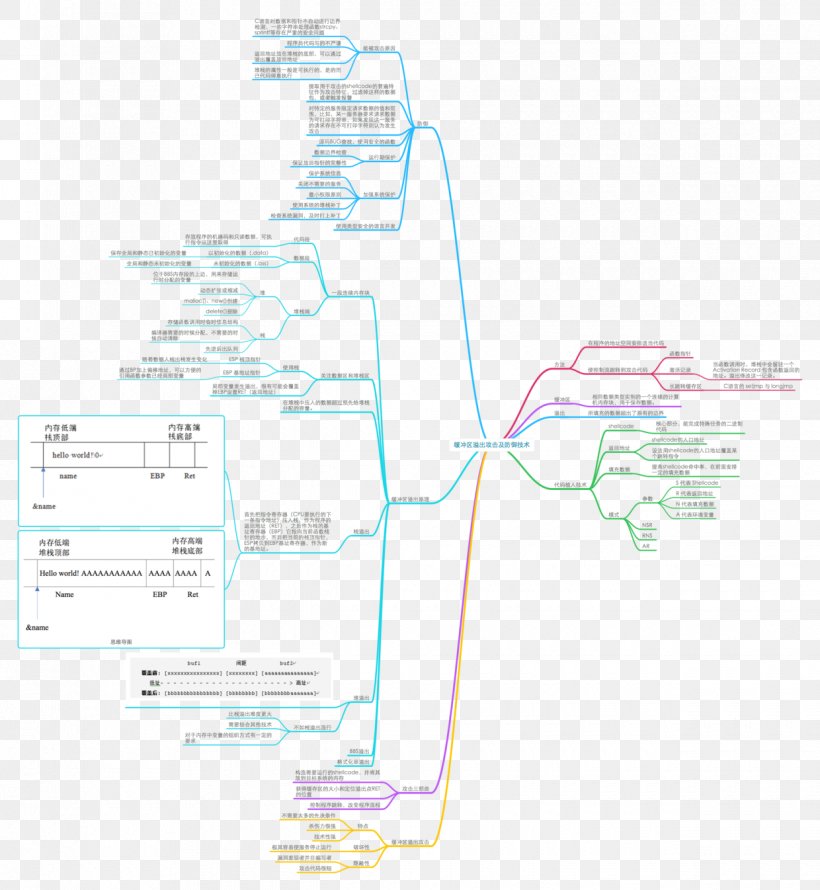
homework3 Stack-based buffer overflow-2 - CSE 610 Special Topics: System Security - Attack and Defense for Binaries Instructor: Ziming | Course Hero

swift - HKWorkoutRouteBuilder and CLLocationManager only adding route updates in increments - Stack Overflow

Lab 3 report.docx - Ankit Kumar 773312668 Buffer Overflow Vulnerability Lab Report Task 1: Non-root stack program Debug stack Figure 1.1 Return address | Course Hero